How to safeguard brand trust with email authentication

“A brand for a company is like a reputation for a person.” – Jeff Bezos.
Imagine what would happen to your reputation if someone stole your identity and started opening bank accounts to commit fraud.
Identity theft is just as much a problem when it comes to email as in the real world—and it happens to businesses every day. It puts brands at risk of spammers spoofing their email addresses to send fake messages that appear to come from them.
The good news is that you can stop scammers in their tracks and prevent them from harming your brand. Learn how to use email authentication methods to safeguard your brand and keep spoofed emails out of the inbox.
What is email authentication?
Email authentication is about validating the identity of the sender of an email—basically, proving that a message is actually sent by whoever appears to be sending it. It uses email validation standards to check that the sender's address isn’t forged and that the email contents have not been modified after sending.
Jeff Bezos, for example, keeps a public email address at jeff@amazon.com for customer feedback! Thanks to authentication, you can be assured that it is indeed Jeff and his team behind the email and that messages received from it are the real deal.
How email authentication works
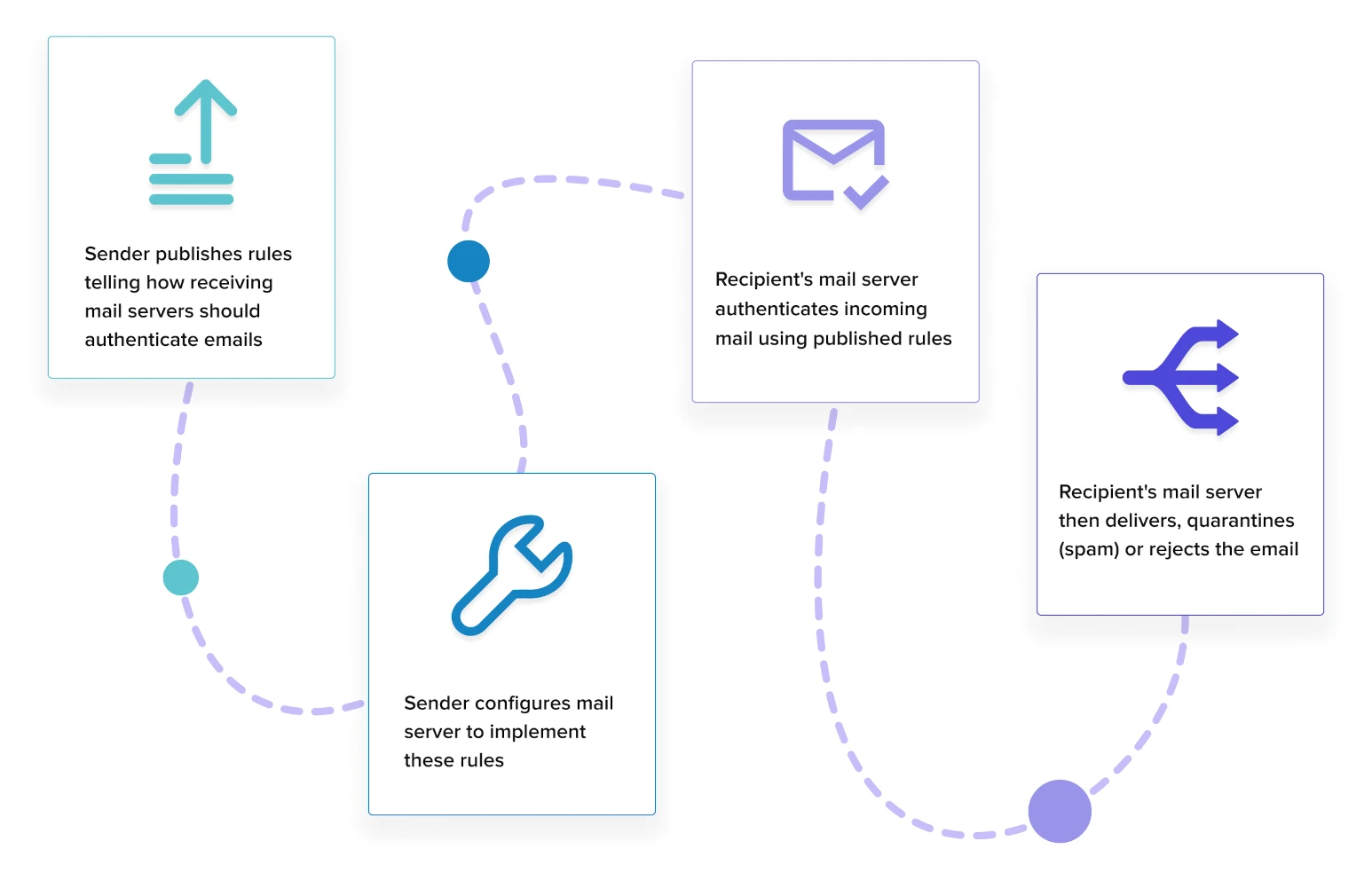
Today, three authentication standards are used to filter spoofed email messages before they reach the inbox: SPF, DKIM, and DMARC. How these email authentication protocols work will be covered in more detail but they follow a general path to verify the sender’s identity:
You publish rules on how to authenticate emails sent from your domain.
Your mail servers are configured to implement and follow these rules.
The receiving mail server checks your mail against the rules that you published.
Your email is then delivered, quarantined in the spam folder, or rejected.
Types of email authentication methods
1. Sender Policy Framework (SPF)
SPF authentication fixes a vulnerability in SMTP where messages can be sent claiming to be from any IP address. To prevent email spoofing, an SPF record is created in your DNS that lists all the mail servers authorized to send email for your domain.
When an email is received, the receiving mail server compares the sending domain with the servers listed in your SPF record. If there’s a match, the message is genuine. Here’s an example of a TXT record for SPF that is used by MailerSend:
v=spf1 include:_spf.mailersend.net ~allThis tells mail servers that MailerSend, a third-party email service provider, is allowed to send transactional emails on the senders’ behalf. Other emails not sent from MailerSend can be marked as spam.
2. DomainKeys Identified Mail (DKIM)
DKIM authentication was developed in response to person-in-the-middle (PITM) attacks where hackers change the contents of emails in transit. Public key cryptography is used to verify that the contents of your email have not been altered after sending it.
Email spoofing is prevented by adding a public key to your DNS. An encrypted digital signature is then added to your message headers using a private key known only to you. When an email is received, the header is decrypted and the DKIM signature is compared to validate the email.
Here’s an example of a CNAME record for DKIM used by MailerSend:
Name:
mlsend2._domainkey.test.comValue:
mlsend2._domainkey.mailersend.ioThis tells mail servers to decrypt the email headers using the public key. What’s more, subdomains are not allowed to send emails on the senders’ behalf, so they should be rejected.
By using CNAME, the DKIM record is a pointer to the key instead of containing the key. This makes DKIM more secure, scalable and flexible.
3. Domain-based Message Authentication Reporting and Conformance (DMARC)
DMARC is an authentication framework that unites SPF and DKIM together with a consistent set of security rules. Along with policies to manage emails that fail authentication, you can also get reports about authentication issues and email activity.
First, an identifier alignment test compares the email’s “From” header with the sending domain using SPF and DKIM methods. Depending on how closely they need to match—which you set with the security rules—the email passes or fails the check.
Next, DMARC policies tell the receiving mail server what to do with unauthenticated emails. They can be delivered (for testing purposes), quarantined (by putting them in the spam folder), or rejected (by sending a bounce message to the sender).
Here’s an example of a TXT record for DMARC:
v=DMARC1; p=none; rua=mailto:aggregate@justanothercompanyname.com; ruf=mailto:forensic@justanothercompanyname.com; fo=1; pct=100; rf=afrfThis DMARC record instructs mail servers not to take any action on emails that have failed SPF or DKIM authentication. It also instructs that reports on email activity and failed authentications be sent to the specified email addresses.
Importance of email authentication
Having a way of verifying email senders will stop spammers from impersonating your brand with fake emails. Better still, it helps to prevent phishing attacks that use spoofed emails to trick recipients into giving up confidential data like logins and passwords.
1. Safeguards your brand
Adding an email authentication layer means that people can be confident about the brand they are interacting with. Also, it avoids negative publicity about losses suffered by victims of malware or phishing scams that were sent with emails using your brand.
2. Protects your sender reputation
Email authentication records tell email providers—like Gmail, Yahoo, Outlook and others—that you are a genuine sender. These records are also tied to your sending domain, giving your sending reputation a boost for ISPs that look closely at domain reputation.
3. Ensures email deliverability
Your ability to land in the inbox suffers when bad actors continue to send fraudulent emails using your brand. When enough people mark these emails as spam, your genuine emails will go straight into the spam folder—or not be delivered at all.
Learn more about deliverability with our email deliverability guide.
No security measures are 100% effective when the weakest link is often human error. While email authentication will stop spammers from using your domain, these illegitimate senders can get creative by registering look-alike domains or sending convincing phishing emails with dodgy domains. Your recipients should double-check URLs before clicking further!
10 email authentication best practices
Use these best practices to safeguard your brand and give recipients the confidence to interact with your emails.
TL;DR Checklist for email authentication best practices
1. Audit your mail servers.
2. Secure your sending domains.
3. Review your DNS records.
4. Implement DMARC gradually.
5. Secure your networks.
6. Analyze email authentication reports.
7. Encrypt traffic between your servers.
8. Secure your DNS.
9. Monitor your IP addresses.
10. Turn on 2FA for accounts.
1. Audit your mail servers
As your sending requirements grow in complexity with your business, you might not know which machines are sending messages on your behalf! Get clarity by creating a spreadsheet of all your mail servers along with their IP addresses and domains. Some of these can include:
Web servers
Mail servers
Internal email servers
Email service providers, such as MailerLite and MailerSend
2. Secure your sending domains
Your domains are brand assets that are critical to your business. Secure your assets by enforcing SPF and DKIM for top-level domains (.com and .net names, for example), parked domains, and other sub-domains that are publicly visible.
If there are attempts to change your DNS records or transfer ownership of your domain, you will need to unlock it first with a one-time password sent by the domain provider.
When you add a new sending domain in MailerSend, you’re protected from the start with auto-generated SPF and DKIM records. 💪
Check out our guide to securing your email and environment.
3. Review your DNS records
For SPF records, check that you have no more than 10 DNS lookups. Exceed this number and you will fail email authentication. This limit was imposed to prevent denial-of-service (DoS) attacks and to conserve the resources of email servers.
Next, test your SPF record by publishing it in test mode. SPF has testing tags that will help you identify missing mail servers in your audit. Once done, turn off test mode to start protecting yourself from spammers!
In MailerSend, SPF defaults to test mode using the ~all tag. You can change it to -all once you are sure that emails are being authenticated correctly.
Finally, publish your SPF and DKIM records to your DNS so that mailbox providers can look them up. Remember, it can take up to 48 hours for DNS changes to be reflected globally. The sooner you publish them, the better it is for your email deliverability.
4. Implement DMARC gradually
When using DMARC for the first time, start it in “monitor” mode so that you can observe and tweak it as you go along. Once you’re satisfied that genuine emails are not getting filtered, you can move to “enforcement” mode to start rejecting and quarantining emails.
You can also test your DMARC policies by using the pct tag. By default, every email is checked (pct=100) but you can set a value between 1-100 until you are confident your policies are working. For example, pct=20 means check 20% of my emails for DMARC compliance.
5. Secure your networks
Now that you have SPF, DKIM and DMARC implemented, make sure that they are enabled across all the networks used by your business. You'll be protected from malicious emails and phishing attacks, thus preventing malware and information theft.
6. Analyze email authentication reports
Look for suspicious activity using two types of DMARC reports: an aggregate report (RUA) and a forensic report (RUF). RUA provides an overview of email traffic while RUF contains details about emails that failed authentication, including their content.
7. Encrypt traffic between your servers
Another vulnerability of SMTP is that emails are sent in plain text format while in transit between email clients. This means that determined hackers can snoop and monitor your messages while they make their way to the recipient!
You can prevent email eavesdropping by turning on Transport Layer Security (TLS), a protocol that encrypts Internet traffic. The good news is that MailerSend enables TLS by default when you use SMTP for outgoing emails.
8. Secure your DNS
The Domain Name System (DNS) is the phonebook of the Internet. It matches human-readable domain names with IP addresses. Like SMTP, the creators of DNS did not prioritize security as the Internet was mainly used by institutions of higher learning.
DNS is still vulnerable to security attacks where hackers forge DNS records and redirect email traffic to a server they control. You can avoid this by implementing Domain Name System Security Extensions (DNSSEC) that help you protect your DNS infrastructure.
More extensive resources on how to secure DNS are available at the DNSSEC website.
9. Monitor your IP addresses
An IP address is a numerical address that identifies a device on the Internet. For email, each mail server will have a unique address assigned to it. Use IP monitoring tools to keep track of the status and availability of your servers as well as suspicious activity.
10. Turn on 2FA for accounts
Human error is the weakest link in any security infrastructure. Turn on two-factor authentication (2FA) for every account, meaning hackers are unable to proceed without a code from an authenticator app or a one-time password sent to your phone.
How to authenticate your emails
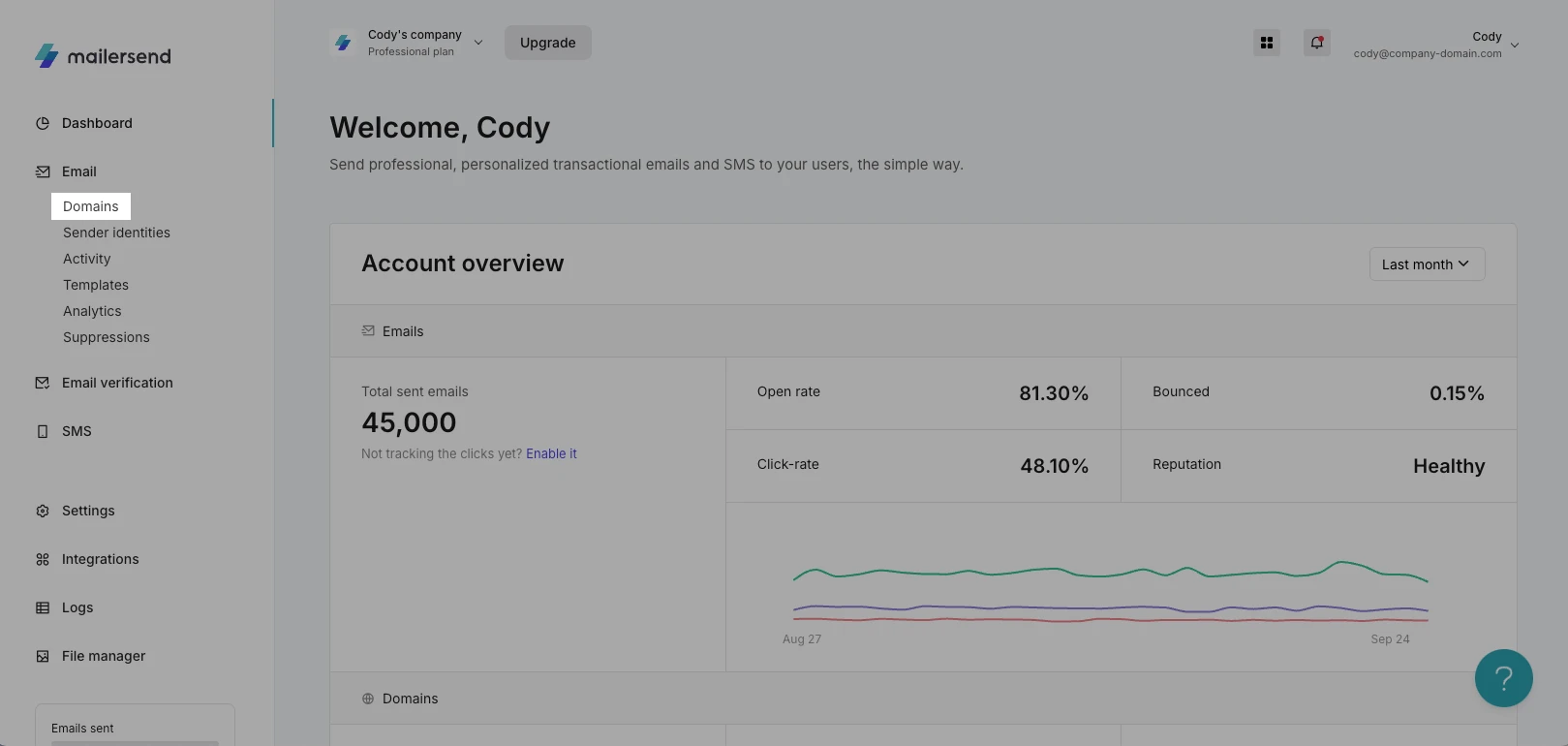
Now it’s time to apply these best practices! To start sending emails with MailerSend from your own domain, you need to verify and authenticate it. Don’t worry, it’s easy and takes only a few minutes.
First, you need to have a MailerSend account as well as access to your domain’s DNS records at your domain or hosting provider.
1. Navigate to Domains on the main dashboard.
2. Click Add domain, enter your domain name, and click Add domain again.
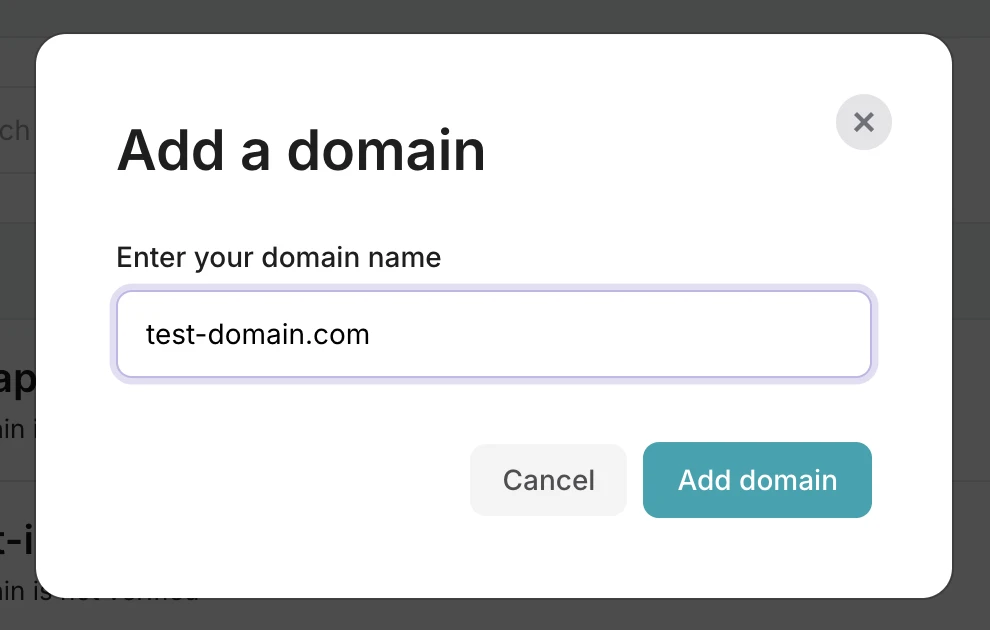
3. A pop-up will appear to automatically connect your domain in a few simple steps. Click Continue to proceed with automatic verification.
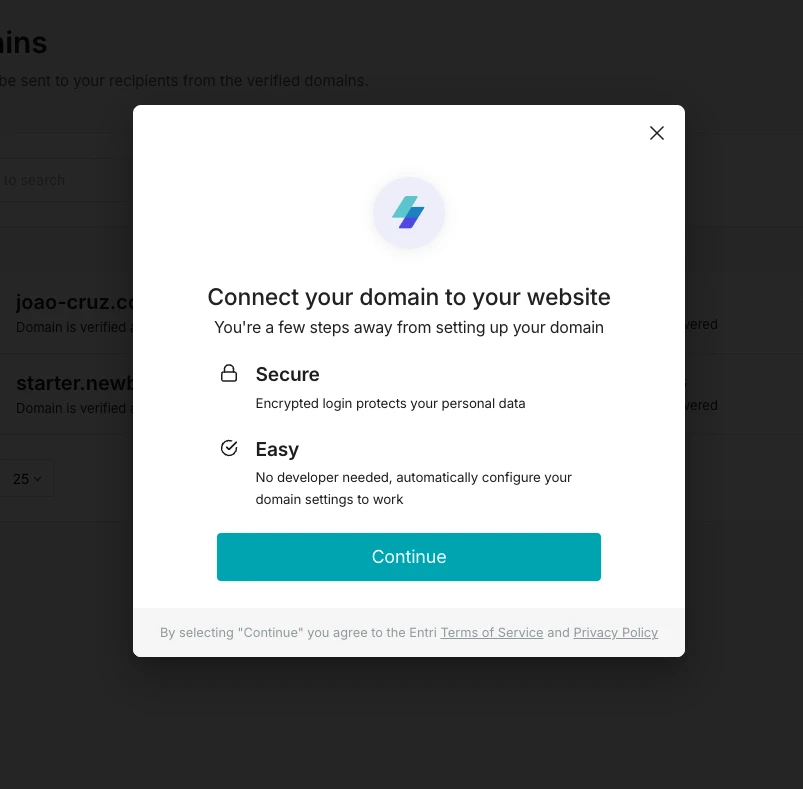
4. If you prefer to verify your domain manually, close the pop-up. You’ll see instructions for adding DNS records to your domain’s DNS page. The exact steps to configure your DNS settings vary with each domain provider. You can find the steps for various providers like GoDaddy, Namecheap and Hostinger in our DNS settings guide.
Alternatively, when you add your domain, MailerSend will automatically detect your domain registrar and provide the specific steps.
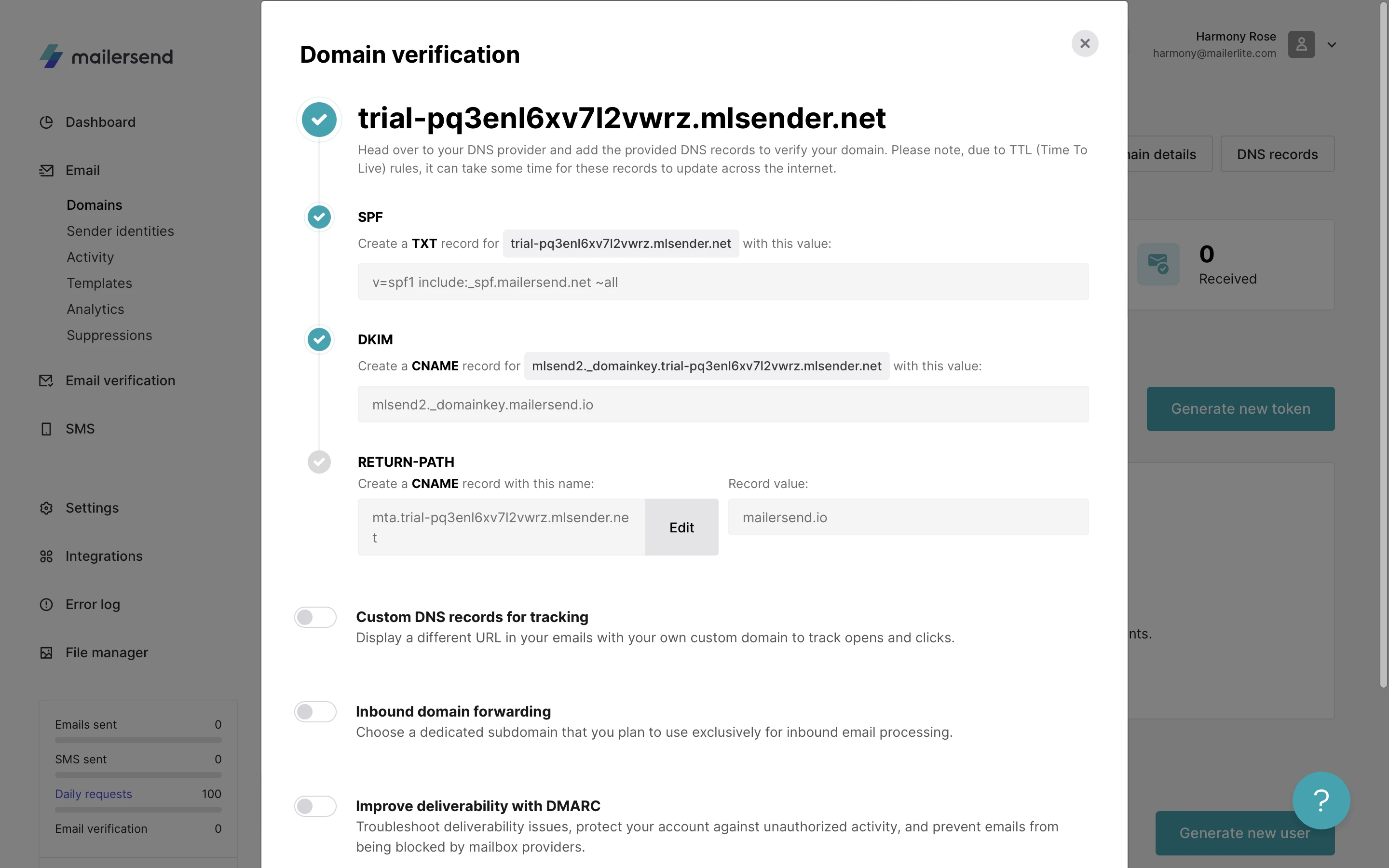
5. Go to the domain’s DNS page at your provider’s site and add the TXT and CNAME records. You can click on each field value in MailerSend to copy it.
If you have multiple SPF records, you’ll need to merge them. Check out our guide on merging SPF records to learn how.
6. After adding the records, jump back to MailerSend to toggle the I have added DNS records option and click Finish verification.
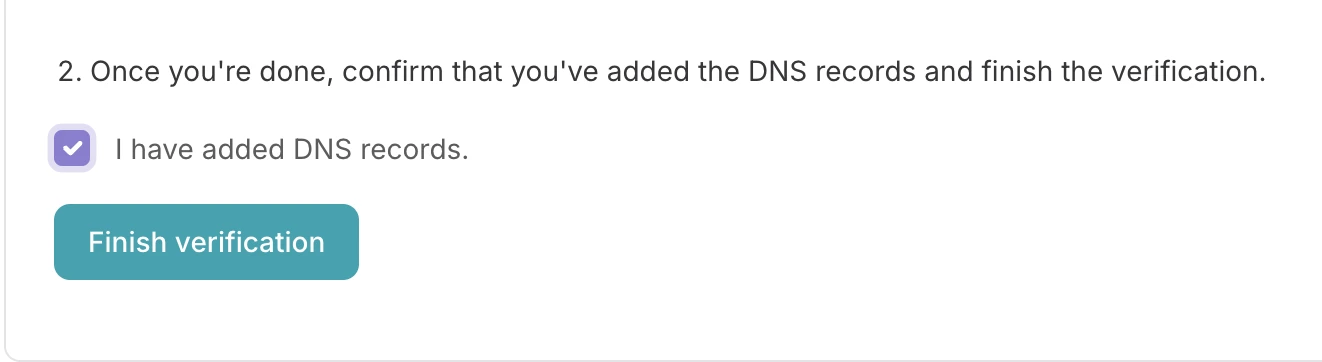
Once the records have been propagated throughout the global DNS servers, your domain will be verified and ready to use!
The DNS changes usually take effect in a few minutes but it may take up to 24-48 hours for the records to update. Here’s a quick troubleshooting guide if your domain is still marked as unverified.
Congratulations on adding and verifying a new domain! The next step is to send emails using MailerSend. Check out our comprehensive how-to guide to start sending.
Protect your business with email authentication
Now that you have the basics of email authentication, start protecting your brand’s reputation from scammers and give customers the confidence of engaging with your emails. Choose a transactional email provider like MailerSend that has email authentication best practices built-in for peace of mind!
More and more businesses are adding DMARC into the mix. Let us know in the comments what your experience has been. 👇
Editor's note: This article was originally published in May 2021, but has been updated with new information and tips.